Help:Access to Toolforge instances with PuTTY and WinSCP
Overview
This page documents Single-click solutions for accessing your Toolforge instances using PuTTY and WinSCP.
- PuTTY is a terminal emulator that has SSH support.
- WinSCP is a Windows GUI for secure file transfer that has SFTP support.
The instructions below can also be used to login with the ssh command in Linux (i.e. ssh username@login.toolforge.org).
For other Cloud VPS projects than tools on Toolforge, instructions differ.
With the correct settings, a single click shell connection or file transfer is possible, and no command line input trouble is needed.
Prerequisites
Information:
USERNAME: your shell username on wikitech and Toolforge (you may find it at Special:Preferences)PATH-TO-YOUR-PRIVATE-KEY: the path and name of your private key file on your local system. You can add your public SSH key in the Toolforge admin console.
Programs:
- PuTTY
- WinSCP
- plink.exe (part of PuTTY suite)
- Pageant (PuTTY authentication agent, part of both the PuTTY and WinSCP suites)
How to set up PuTTY for direct access to your Toolforge account
You are likely going to set up connections to each of the login servers:
Make sure private key is compatible with putty. Sometimes you need to convert it using puttygen or generate keys in PuTTY.
The remaining configuration options are identical for all login servers. Of course, you may prefer screen and scroll buffer sizes of your choice:
Adding a keep-alive time will prevent your connection from dropping when inactive.
In order to start the webservice, input the following commands:
$ become PROJECT-NAME
$ mkdir public_html
$ webservice start
Use webservice --help to get a full list of arguments.
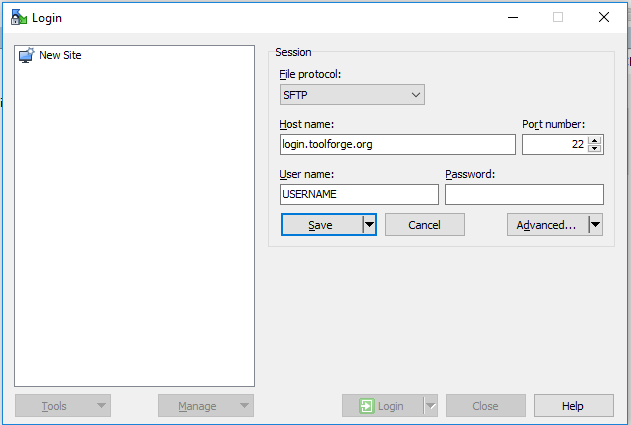
How to set up WinSCP for direct access to your Toolforge account
With WinSCP you must setup a site pointing to the adequate hostname and change the advanced settings to use your private key file on the authentication tab.

/data/project/PROJECT-NAME
sudo -u tools.PROJECT-NAME /usr/lib/sftp-server
Troubleshooting permissions errors
Sometimes the file system permissions on the tool's directory (/data/project/$TOOL) can get messed up and be missing the group write permission. You can check the current permissions by logging into a bastion and showing the directory:
$ ssh login.toolforge.org
$ ls -ld /data/project/bd808-test
drwxrwsr-x 7 tools.bd808-test tools.bd808-test 4096 Jul 19 15:07 /data/project/bd808-test/
The "drwxrwsr-x" section in the output above is the directory permissions. Each letter tells you something about the permissions mask on the file system:
- "d" - this is a directory.
- "rwx" - These are the permissions for the directory's owning user. "r" - read, "w" - write, "x" - eXecute.
- "rws" - These are the permissions for the directory's owning group. "r" - read, "w" - write, "s" - sticky. Sticky implies execute and also attempts to set the same group ownership on all new files and directories created inside the directory.
- "r-x" - These are the permissions for "other" users (users who are not the owner or in the owning group). The "-" means that other users cannot write to this directory.
Your user will be a member of the owning group for the directory. When you cannot upload files the problem is often that the "w" write permission is missing for the group on either the tool's directory itself or on a subdirectory or file that you are trying to change. Fixing that is as easy as logging into a bastion, becoming the tool, and changing the permissions:
$ ssh login.toolforge.org
$ become $MY_TOOL
$ chmod -R g+w /data/project/$MY_TOOL
# Recusively grant write permission to the group on all files and directories.
FileZilla
You may also like to use FileZilla for managing files in the remote directory. FileZilla supports SFTP and Putty SSH keys and can be configured with the same configuration settings as above for WinScp. See How to put your SSH key to FileZilla. However, FileZilla lacks the feature of on-login "sudo" SSH command unfortunately. So, you'll stay without "become PROJECT-NAME" forever and your experience won't be very comfortable. There's an issue at FileZilla support site.
You can however route the location to that of your project, and that can be done by replacing it with (usually)/data/project/project_name.
Communication and support
Support and administration of the WMCS resources is provided by the Wikimedia Foundation Cloud Services team and Wikimedia movement volunteers. Please reach out with questions and join the conversation:
- Chat in real time in the IRC channel #wikimedia-cloud connect or the bridged Telegram group
- Discuss via email after you have subscribed to the cloud@ mailing list
- Subscribe to the cloud-announce@ mailing list (all messages are also mirrored to the cloud@ list)
- Read the News wiki page
Use a subproject of the #Cloud-Services Phabricator project to track confirmed bug reports and feature requests about the Cloud Services infrastructure itself
Read the Cloud Services Blog (for the broader Wikimedia movement, see the Wikimedia Technical Blog)